SQL: Making T-SQL Scripts Easier to Read
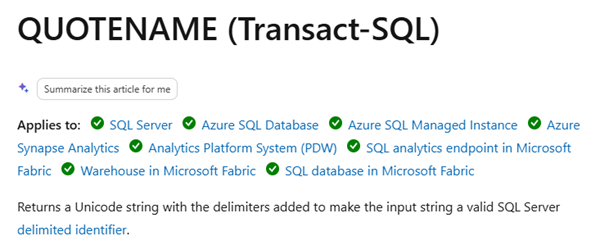
When creating tools that script out SQL Server objects, the normal behavior is to quote object names, in case the names wouldn’t otherwise be valid. The problem with that, is that many scripts then become an amazing mess of square brackets that makes the scripts far less readable. And often, there’s no need for the quoting in the first place.
If you avoid things like spaces in object names, you can mostly get away without quoting i.e. Sales.Customers is just fine and doesn’t need to be [Sales].[Customers]. That’s just far less readable IMHO.
2026-05-20